Free Tool
How Susceptible is Your Corporate Environment to the SSID Stripping Vulnerability?
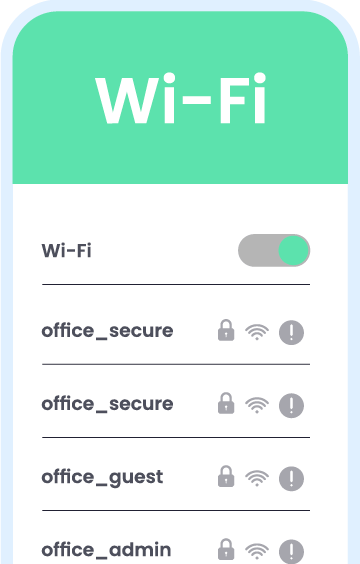
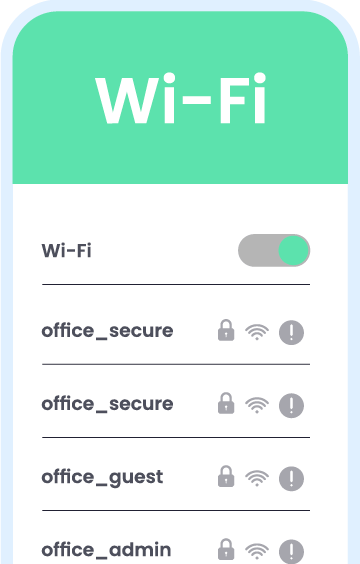
SSID Stripping is a new vulnerability that affects the way some wireless network names are displayed. As a consequence, unsuspecting users may connect to an attacker-controlled network they did not intend to connect to.
The SSID Stripping vulnerability affects all major software platforms – Microsoft Windows, Apple iOS and macOS, Android and Ubuntu.
Hide ’n Seek is a free tool by AirEye that helps organizations assess how vulnerable their corporate devices are to SSID Stripping.
Download now this simple Windows application, and:
For any questions or comments on the tool, please email: [email protected].

Click here for a 25-sec short video showing how to run the tool.
The HideNSeek tool acts as an indicator that your device is at risk to the SSID-Stripping vulnerability so there is no need to connect.
That said, if you still want to connect, use the password: 12345678
The tool identifies a connection to an SSID Stripping network and terminates it immediately.
Note that the SSID Stripping name will continue to broadcast until the timeout. In order to avoid reconnecting, make sure that the auto-connect to that network is turned off.
The tool creates a mobile hotspot on the Windows device with the SSID Stripping name.
The hotspot remains on until the timeout. However, if someone connects to that network, the hotspot turns off for a few seconds, and automatically turns back on with the same SSID Stripping name.
This is an operating system related issue that has to do with the refreshing of network list names. It will be removed from the display within a few minutes at most.
Please email [email protected].