Recently passengers of a flight from Israel to Turkey received on their mobile phones pictures of airplane crashes, causing fright and leading the pilot to return to the terminal. After a security examination, 9 passengers were arrested and the flight took off again.
While the offenders considered this a prank, it is a type of an Over the Air (OTA) Attack. OTA attacks exist and have grave consequences that organizations must be aware of.
How did this happen?
The offending passengers utilized Apple’s feature, AirDrop, to send the files. The AirDrop protocol enables two devices to directly communicate without needing a pure Wi-Fi connection or Internet access which is provided by an Access Point (AP). This type of Peer-to-Peer connection is based on a common and standardized protocol called Wi-Fi Direct.
Given the prevalence of Wi-Fi enabled devices – and these are not just iPhones, but can also be vehicles, monitors, printers, medical devices, robotic machinery and obviously also laptops and traditional IT systems – hackers can access any other Wi-Fi enabled device in the same network airspace, remotely take control of them and further take advantage of the newly controlled device to hop over-the-air to other devices in the network airspace.
How big is your network airspace threat surface? Just check Wigle.net
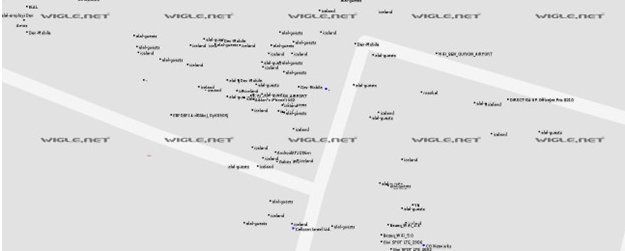
To illustrate the prevalence of accessible Wi-Fi enabled devices, just take a look at Wigle.net. This is a free tool that as of now mapped nearly 12.5B(!) Wi-Fi devices across the world according to their MAC addresses, including those in office and building spaces.
This tool is handy for anyone searching for a Wi-Fi connection (and how many times did you need that for yourself?) but as with a lot of cases to do good, hackers are quick to take advantage of such rich data.
Take a look at the airport’s network airspace in Wigle.net, an attacker can glean initial intelligence on the network airspace attack surface:
An attacker interested to exploit one of the devices in its vicinity can access another device through it, or send an AirDrop message to any other device in its vicinity.
Over the Air (OTA) Attacks can be Remotely Exploited
While the offenders in the airplane case were on the airplane, it’s important to note that OTA attacks can be exploited remotely – without actually physically being in the network airspace.
The concept is similar. The attacker remotely takes control of a device in the network airspace of the target, what we also call an Antenna for Hire, and hop to a Wi-Fi enabled device in its network airspace. Finding that Antenna for Hire can also easily be done via Wigle.net or other freely available tools. Then, pop in the details of that Antenna for Hire into Shodan or a vulnerability database, and attacking that Antenna for Hire is straightforward.
Over the Air Attacks are a Business Issue
This is not a limited consumer issue. OTA attacks can happen in any type of environment – think banks, hospitals, factories, tech companies… any company, in any vertical.
The reason is that the corporate network airspace is swarmed with Antenna for Hire. Once under the attacker’s control, it becomes a threat to other devices in its vicinity.
Since an Antenna for Hire is not necessarily under your security control, there is nothing you can do about it – even if you know it has been hacked. Consider that garage across the street of your headquarters with their security camera. Say you know that camera was hacked. You are even aware that it’s broadcasting a similar network name as your company to fool users to connect to it. Your hands are tied – apart from knocking on the garage’s manager to remove that security camera, there’s nothing for you to do against Antenna for Hire.
Back to the corporate environment, consider your printer that is connected on one end to the corporate network and on the other, broadcasting Wi-Fi Direct. The attacker, remotely, via an Antenna for Hire, takes advantage of the Wi-Fi connection and takes control of the printer and gains direct access to the corporate network. In this manner, the attacker bypasses existing network security solutions such as NAC, IDS, Firewalls, etc.
Not a bug, but a feature
The utilization of AirDrop, Wi-Fi Direct, and Wi-Fi for that matter, is certainly not a vulnerability or a bug. It’s just the way the protocol works, and hence cannot be fixed.
What are organizations doing?
Considering that OTA attacks bypass all traditional network security solutions, a new network security category has emerged called Network Airspace Control and Protection (NACP).
As their name implies, NACP solutions look the organization’s network airspace and identify all broadcasting devices. They then classify what is a corporate asset and what is an Antenna for Hire. Based on the wireless security policy, they stop connections that violate the policy. At the most basic level – they terminate any connection attempt between an Antenna for Hire and a corporate asset.
How does your network airspace look like?
As a first step, we recommend you registering to Wigle.net and check your corporate network airspace (you need to register to see all the devices). Most chances are you’ll find devices and access points listed you weren’t aware of as well as Antenna for Hire in your vicinity.
If you’d like to hear more about your network airspace and how AirEye’s NACP solution can help, contact us for a demo today.

