WPA3 & OWE: Are We Truly Secure in Modern Wireless Environments?
Emerging Wireless Standards Promise Better Security, But New Threats Are Already Here The wireless landscape is evolving rapidly, with new protocols like WPA3 and Opportunistic Wireless Encryption (OWE) designed to address longstanding vulnerabilities in Wi-Fi security. But as with every technological advancement, attackers are quick to adapt. The question organizations must ask: Are these new […]
Rogue Access Points Are Back — And Smarter Than Ever

They were one of the first wireless threats ever documented. Simple, crude, and often misconfigured — rogue access points used to be the rookie mistake of the early 2000s. But today? They’re back. And they’ve evolved. What was once the domain of interns plugging in Wi-Fi routers “for convenience” is now the playground of red […]
The Wireless Security Wake-Up Call: What EDR, NDR & XDR Still Miss

April 2025 | By the AirEye Team If your EDR, NDR, or even XDR solution isn’t watching your Network Airspace, your perimeter is already broken. Our recent Wireless Airspace Threat Modeling guide sent a clear message: Attackers are exploiting the wireless layer because no one’s watching it. “You can’t stop what you can’t see. And […]
Threat Modeling the Wireless Airspace in 2025

“Any Wi-Fi Attack Can Now Be a Remote Attack” By the AirEye Research TeamInspired by Mathy Vanhoef’s insights 1. Objective Wireless threats are no longer bound to physical proximity. Pre-auth vulnerabilities, beacon spoofing, and rogue access points can now be exploited remotely — even globally — thanks to cloud relays, malicious proxies, and antenna-for-hire models. […]
Wi-Fi Attacks: From White Vans, to Drones and on to Antenna for Hire
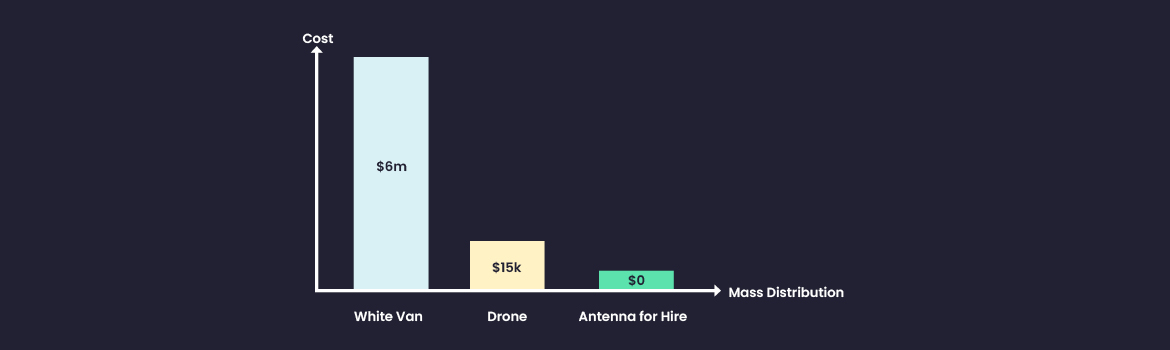
Earlier this week Greg Linares published research on a real-life Wi-Fi cyberattack against an east coast based private equity firm. The origin of the attack was a drone
First-hand Account of an Anatomy of a Wireless Attack/ Hedgehog Security
Peter Bassill from Incident Response firm, Hedgehog Security, relayed to us the following fascinating anatomy of a wireless (aka over-the-air) attack at a UK healthcare organization
AirDrop: The Hackers Tool for Dummies

Recently passengers of a flight from Israel to Turkey received on their mobile phones pictures of airplane crashes, causing fright and leading the
Trends in Wi-Fi Vulnerabilities: This Time, It’s Qualcomm
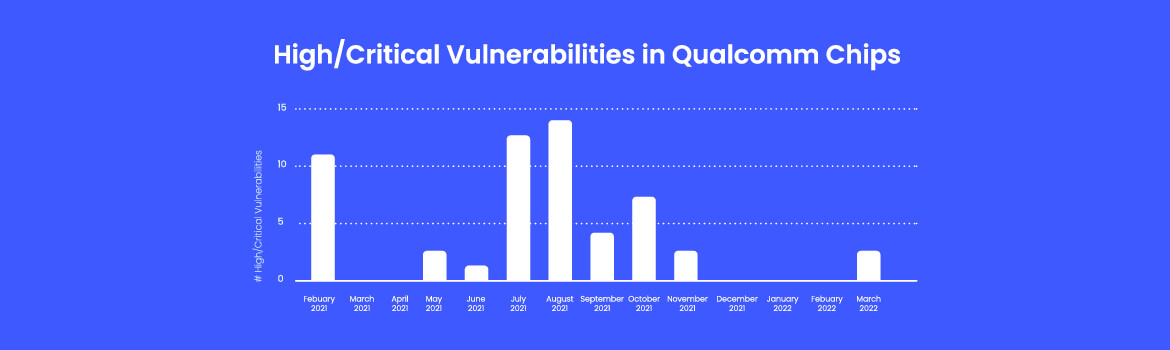
Qualcomm’s monthly security bulletins show an interesting trend with their Wi-Fi chips, which for some reason hardly receive any attention.
The Intel Vulnerabilities Disclosure: They Actually Can be Remotely Exploitable
Late last week, Intel issued security advisories, INTEL-SA-00539, INTEL-SA-00581, INTEL-SA-00582
FragAttacks + Antenna for Hire: The Perfect Storm in Your Network Airspace
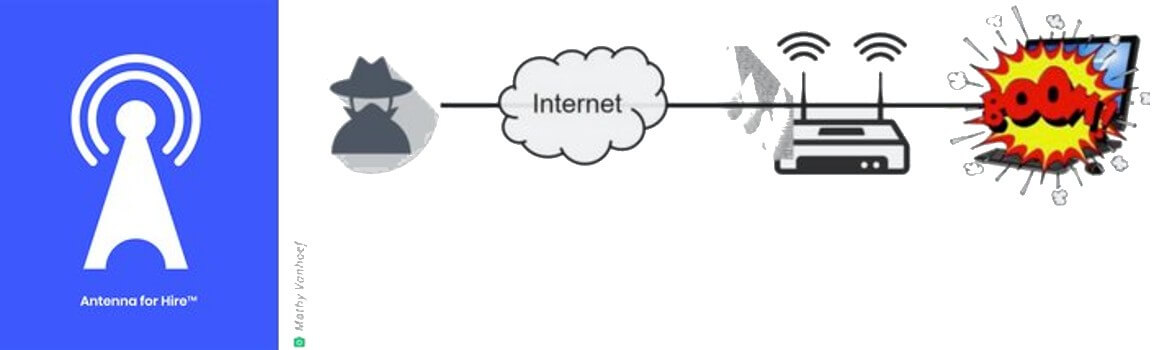
Coupling FragAttacks with Antenna for Hire means that the attacks can be carried out remotely
